Binging Is an Example of a Footprinting Tool Which Uses
An Ethical hacker has to spend the majority of his time in profiling an organization gathering information about the host network and people related to the organization. Learn as much as you can about a system its remote access capabilities its ports and.

5 Ways To Use Padlet In A Higher Ed Online Classroom Online Education Blog Of Touro College
The purpose of footprinting to.

. About computer systems and the companies they belong to. Footinprinting is the gathering of info relating to an intended target. Question 3 5 5 points SNMP uses which of the following ports.
This particular tool can be used for cross domain footprinting for Web 20 applications site discovery reverse lookup host enumeration etc. News on mergers and acquisitions. Refers to the process of collecting as much as information as possible about the target system to find ways to penetrate into the system.
Company contact names email addresses and phone numbers. Net Framework Bing API DNS Reverse Lookups Question 16 5 points Question 16 Unsaved What is the second part of the TCP 3 way handshake. By using a combination of tools and techniques coupled with a healthy dose of patience attackers can take an unknown entity for example XYZ Organization and reduce it to specific.
- DNS - Bing API - Net Framework - Reverse Lookups. Binging is a simple tool to query Bing search engine. Network administrators do not take lightly the probing of their networks and may respond aggressively to.
Footprinting is a part of reconnaissance process which is used for gathering possible information about a target computer system or network. Company deals and other parties involved. Footprinting is all about seeking out information that can be used to facilitate an attack.
Although no longer updated it helped move this genre of tools forward. One can use various different directives like site ip etc. Net Framework Bing API DNS Reverse Lookups Upload your study docs or become a.
Whois SmartWhois NsLookup Sam Spade Whois The primary tool to navigate these databases is Whois. When used in the computer security lexicon Footprinting generally refers to one of the pre. The idea is to gather as much information about the target as possible before starting an attack.
By first footprinting the target a hacker can eliminate tools which will not work against the target systems or network. This information is the first road for the hacker to crack a system. Use tools such as Xprobe2 Winfingerprint and Amap.
- Webserver software Version -. It will use your Bing API key and fetch multiple results. Tools Used in Footprinting.
Phone Numbers and Addresses. The systematic and methodical Footprinting of an organization enables attackers to create a complete profile of an organizations security posture. Other Techniques Used in Footprinting.
Footprinting is the first and most convenient way that hackers use to gather information. Even some target specific information like Operating system details IP. One of the first tools to actually be widely used for active fingerprinting back in the late 1990s was Queso.
This information is very useful to a hacker who is trying to crack a whole system. Footprinting may also involve collecting information such as. Common toolsresources used in the footprinting phase are.
This is a passive information gathering process where we gather information about the target from social media search engines various websites etc. Reviewing a companys website is an example of passive footprinting whereas attempting to gain access to sensitive information through social engineering is an example of active. You should be very careful in using these tools outside of the Lab.
Question 14 options. Enumerate a domain and pull back up to 40K subdomains results are available in an XLS for easy reference. Question 4 5 5 points This vulnerability scanner is from Microsoft.
Footprinting employs the first two steps of reconnaissance gathering the initial target information and determining the network range of the target. Following are the common set of tools used in footprinting. To get this information a hacker might use various tools and technologies.
ACK SYN URG PSH Question 15 5 points Question 15 Unsaved Binging is an example of a footprinting tool which uses _____ to perform queries. By using these footprinting tools a hacker can gain some basic information on or footprint the target. Footprinting and scanning tools This is a selection of footprinting and scanning tools you may wish to install in your MIS Lab machine in order to do the course assignments.
Active Fingerprinting Tools Objective. Information gathered includes name personal details geographical location detrails login pages intranet portals etc. Footprinting means gathering information about a target system which can be used to execute a successful cyber attack.
Question 15 5 points Question 15 Unsaved Binging is an example of a footprinting tool which uses _____ to perform queries. On top of it tool provides. Educate employees to use pseudonyms on blogs groups or forums do not reveal critical infolimit what you publish online use footprinting techniques to discover and remove any publicly available information prevent search engines from caching an webpage and use anonymous registration services do not enable protocols that are not required.
Repeating the same process for pentestlabin it will search for its DNS recordFrom the given screenshot you. Information such as ip address Whois records DNS. Reverse LookupsNet Framework DNS Bing API.
Question 2 5 5 points Binging is an example of a footprinting tool which uses _____ to perform queries. Footprinting could be both passive and active. Footprinting through Search Engines.
In this lesson youll learn more about this term what its uses are what information is gathered and. As an example if a graphics design firm uses all Macintosh computers then all hacking software that targets. There are two types of footprinting as following below.
Services and the aspects of its security. Choose all that apply 22 161 445 162. It is also an online use for DNS footprinting.
Footprinting is the technique used for gathering information about computer systems and the entities they belong to. To get this information a hacker might use various methods with variant tools. And run queries against the engine.
The website zabasearch provides what type of information to users. Binging is an example of a footprinting tool which uses _____ to perform queries. Which of the following best describes footprinting.

Nutrients Free Full Text The Effect Of Religious Dietary Cultures On Food Nitrogen And Phosphorus Footprints A Case Study Of India Html

Education Relationships Play By Fundacja Rozwoju Systemu Edukacji Issuu

Pdf Binge Watching Bears Efficacy Of Real Vs Virtual Flagship Exposure
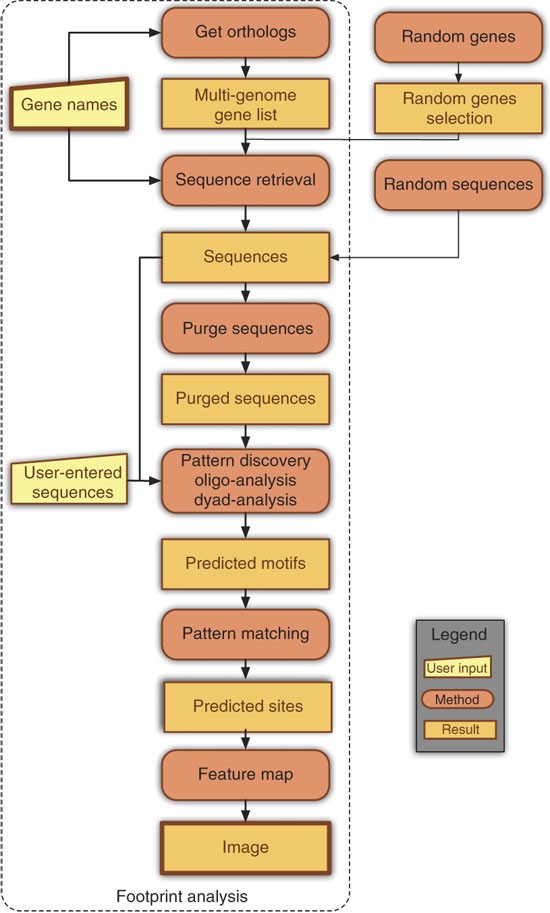
Using Rsat Oligo Analysis And Dyad Analysis Tools To Discover Regulatory Signals In Nucleic Sequences Nature Protocols
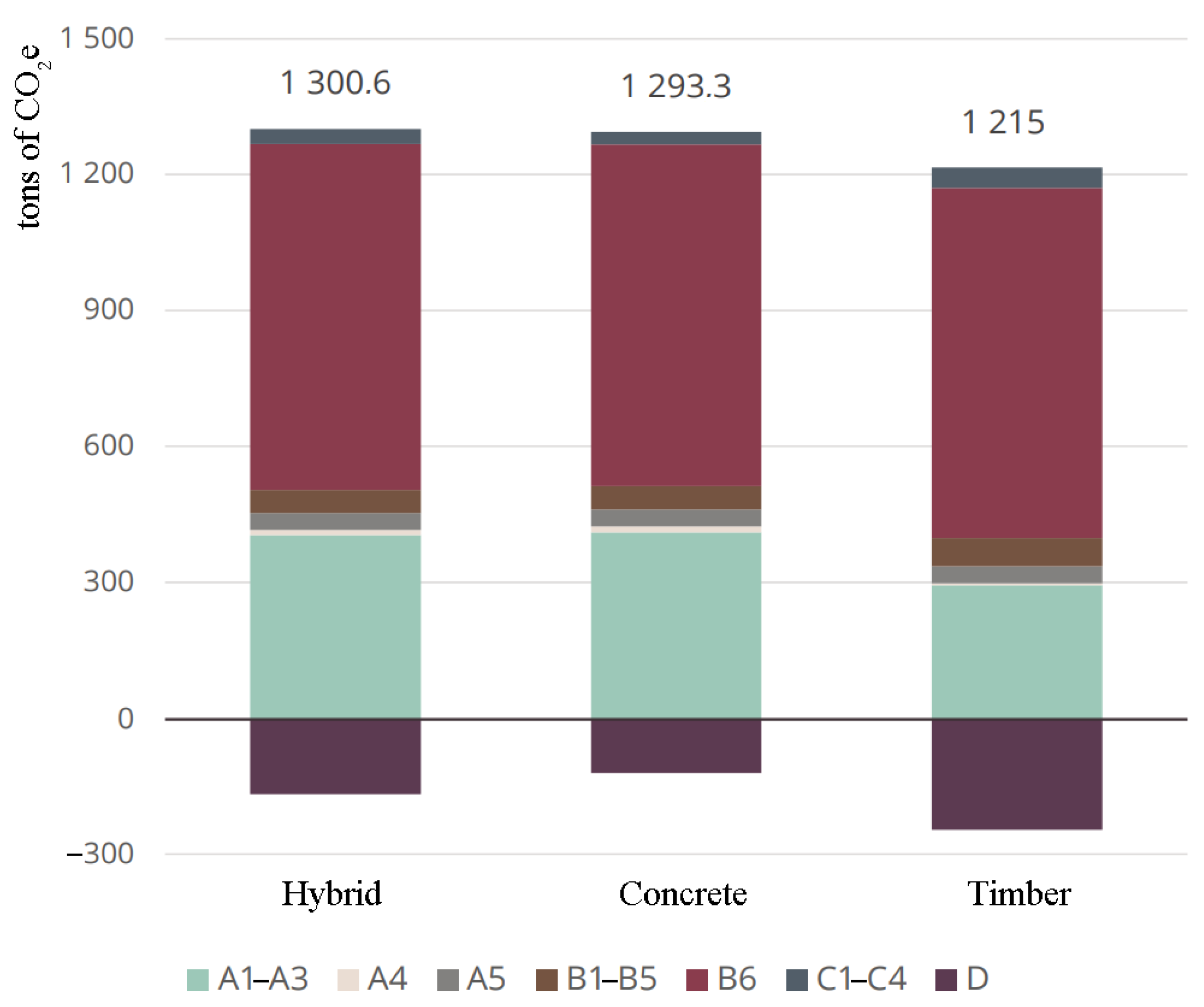
Ijerph Free Full Text Comparative Study On Life Cycle Assessment And Carbon Footprint Of Hybrid Concrete And Timber Apartment Buildings In Finland Html
Pdf Footprint Functional Tools For Pesticide Risk Assessment And Management Www Eu Footprint Org
Pdf Giving Legs To Handprint Thinking Foundations For Evaluating The Good We Do

Pdf Dietary Restriction Behaviors And Binge Eating In Anorexia Nervosa Bulimia Nervosa And Binge Eating Disorder Trans Diagnostic Examination Of The Restraint Model
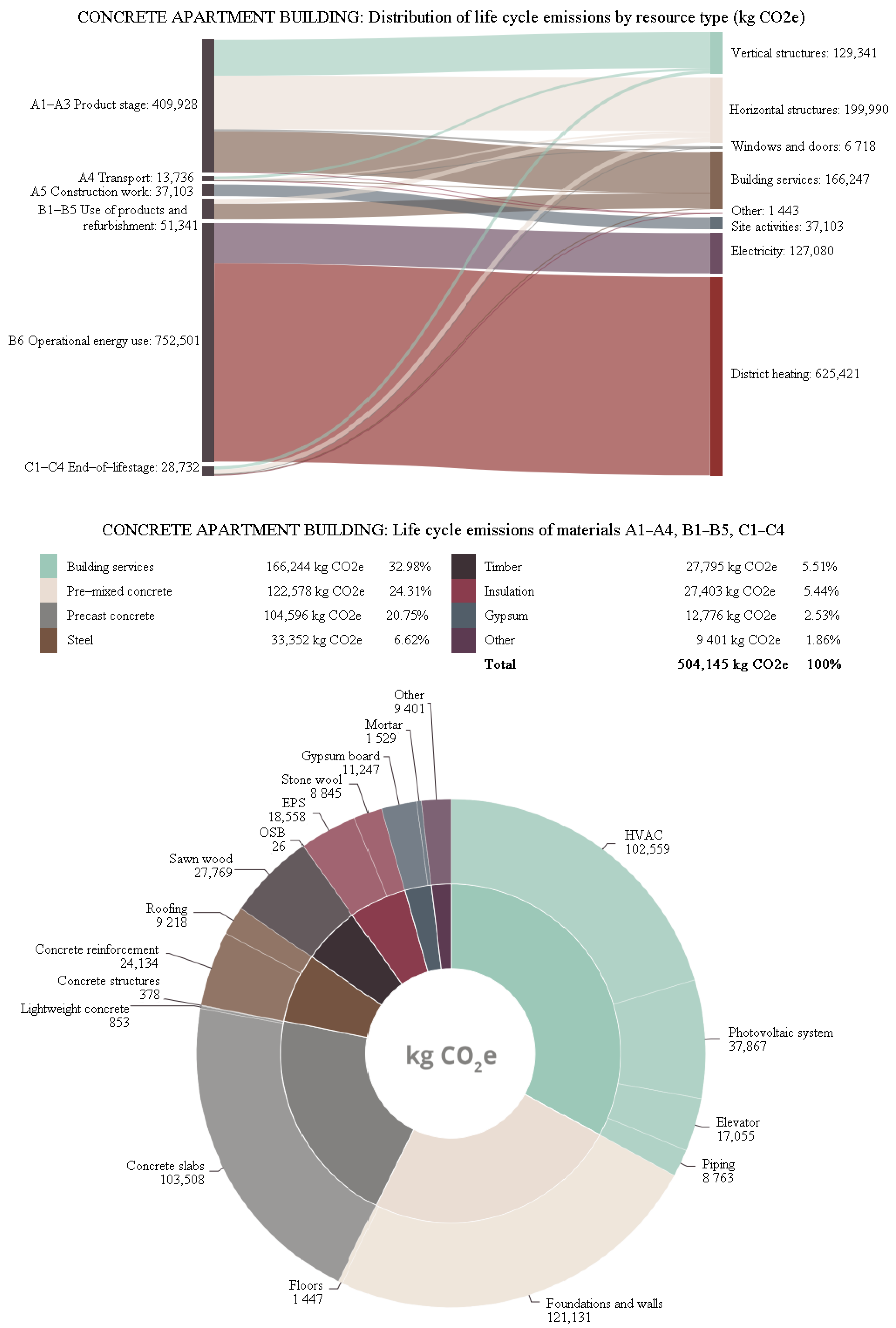
Ijerph Free Full Text Comparative Study On Life Cycle Assessment And Carbon Footprint Of Hybrid Concrete And Timber Apartment Buildings In Finland Html
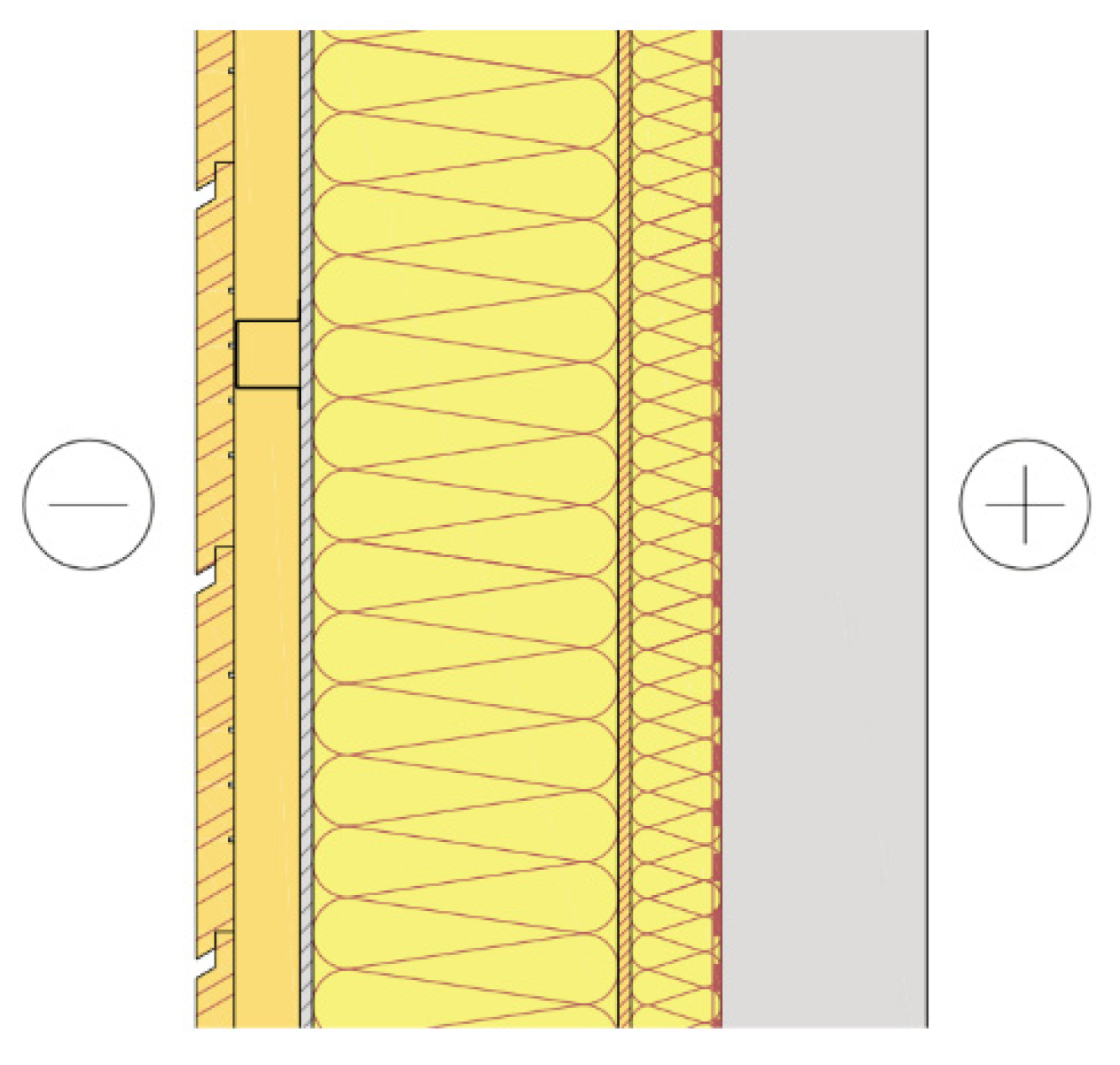
Ijerph Free Full Text Comparative Study On Life Cycle Assessment And Carbon Footprint Of Hybrid Concrete And Timber Apartment Buildings In Finland Html
8 Benefits Of Using Big Data For Businesses

From Beer To Ironing Shirts The Carbon Footprint Of Daily Activities Ecomatcher

Pdf Tools For Collecting Volatile Data A Survey Study
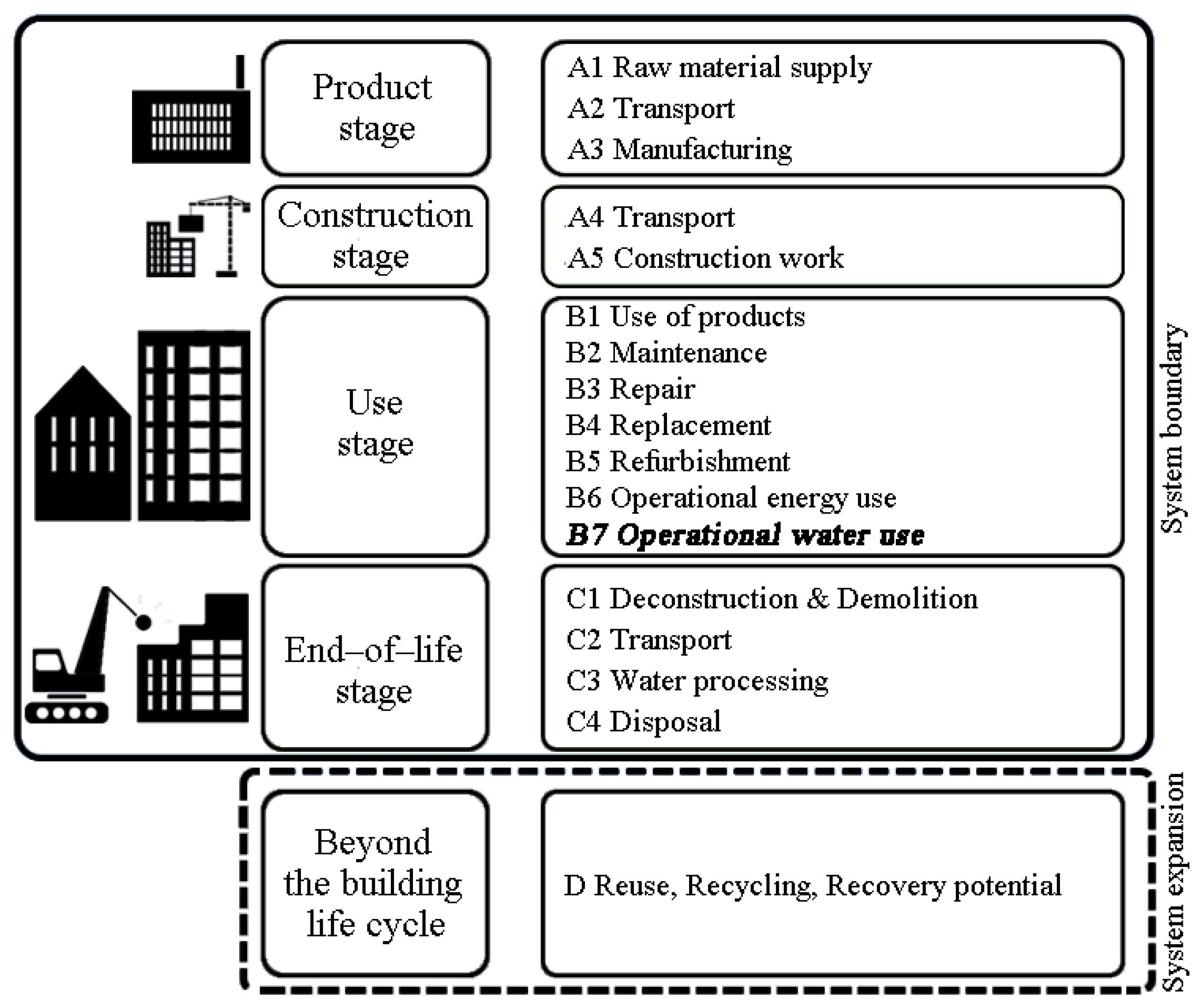
Ijerph Free Full Text Comparative Study On Life Cycle Assessment And Carbon Footprint Of Hybrid Concrete And Timber Apartment Buildings In Finland Html
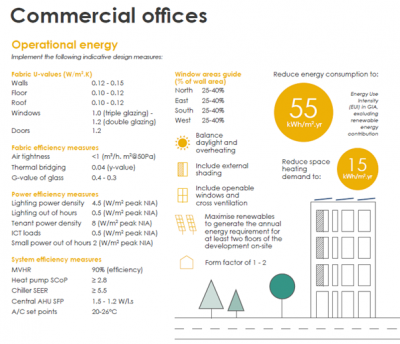
Operational Carbon Steelconstruction Info
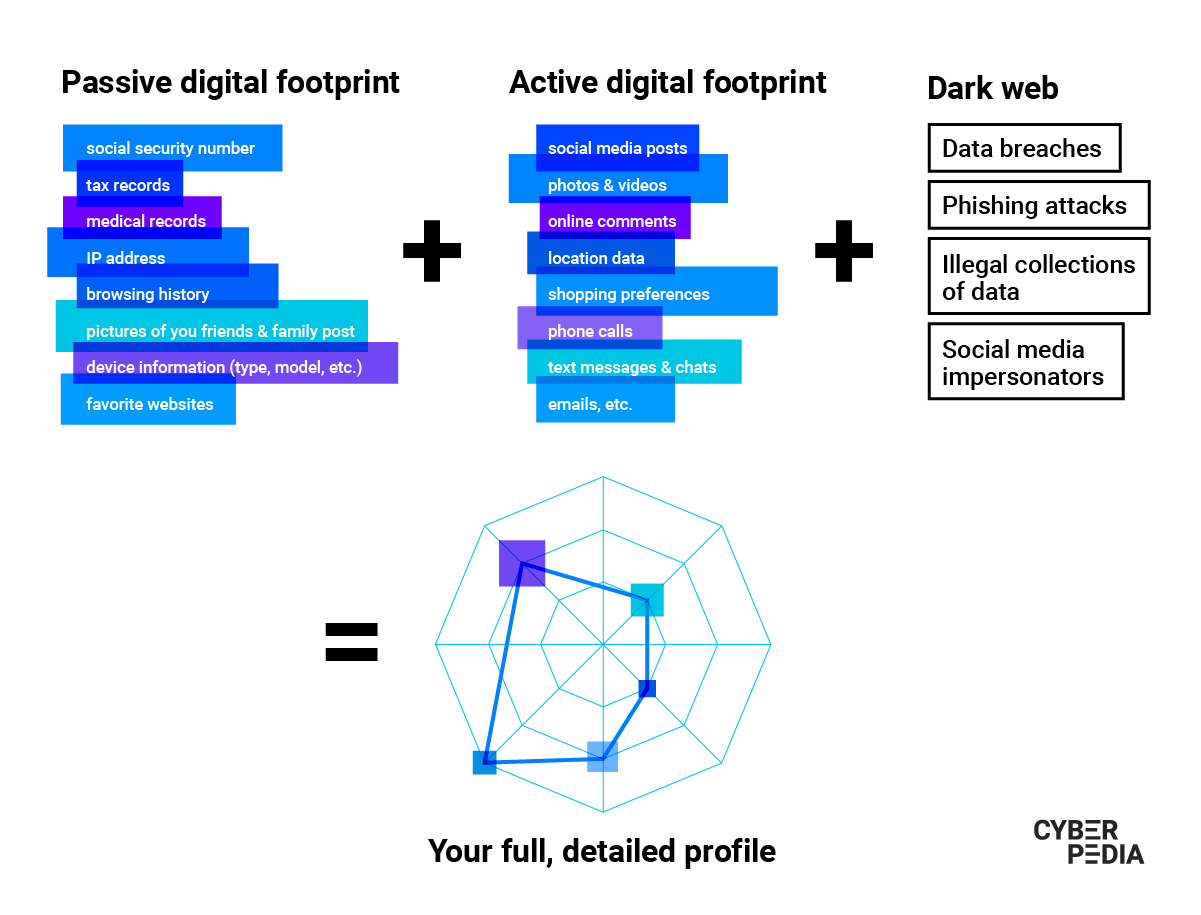
How To Protect Your Digital Footprint Bitdefender Cyberpedia

Pdf Rsat Regulatory Sequence Analysis Tools

Biohydrogen And Biomethane Production From Food Waste Using A Two Stage Dynamic Membrane Bioreactor Dmbr System Sciencedirect
Comments
Post a Comment